This article is written by Shruti Gupta, pursuing a Diploma in Cyber Law, Fintech Regulations and Technology Contracts from Lawsikho.
Table of Contents
Introduction
India has been a favorite hub for cybercriminals, mostly hackers and other malevolent users who misuse the Internet by committing crimes. In the year 2012 to 2018, there had been 90,000 cyber-crime incidents registered in India; out of which over 27,000 cases were registered in the year 2018 alone, marking an increase of more than 121% since 2016.[1] Such an increase in the number of cyber-crimes cases could pose serious economic and national security challenges.
As per 2019 NortonLifeLock Cyber Safety Insights Report, 63% Indians do not know what they will do if their identities are stolen, even though 70% are worried that identities will be stolen. 4 in 10 consumers in India have experienced identity theft.[2] Cyber-crimes know no borders and grow at a pace at par with emerging technologies.
What is a cyber-crime
In any statute, the term cybercrime is not defined. Any unauthorized/ unlawful act, commissioned with the use of a computer or computer network or communication device, to commit or facilitate the crime is called cyber-crime.
Below are the some of the examples of cyber-crimes:
|
CHILD PORNOGRAPHY / CHILD SEXUALLY ABUSIVE MATERIAL (CSAM)
|
CSAM refers to content having an image of sexual in nature, of a child, abused or sexually exploited. Section 67 (B) of the Information Technology Act states that publishing/transmitting any material, in electronic form, portraying children in sexually explicit acts, is a punishable cyber-crime. |
|
CYBER BULLYING
|
A bullying or a form of harassment perpetrated through electronic media or communication devices such as laptop, computer, mobile phone etc. |
|
CYBER STALKING |
• It is the use of electronic media by a person to track a person or tries to communicate/ contact another person to impose personal interaction continually despite the reluctance and disinterest by such person; • To monitor the email, internet or any other form of electronic communication of the other person and thereby committing an offence of stalking. |
|
ONLINE JOB FRAUD |
Wherein a person who is in need of a job is duped for money or defrauded by giving him/her fake promises to employment with higher wages through electronic communication. |
|
ONLINE SEXTORTION
|
When someone threatens to circulate or publish any sensitive/ private material/ images/ content using electronic medium if the other person rejects or denies providing images, favors of sexual nature or money. |
|
VISHING
|
Fraudsters try to obtain personal information like bank account password, customer ID, ATM PIN, OTP, credit card CVV etc. over a phone call. |
|
PHISHING |
It is a type of fraud that involves stealing of personal information of a person such as a bank’s customer ID, Credit Card/ Debit Card number, CVV number, etc. through electronic channels that seem to be from a genuine source. |
|
RANSOMWARE
|
• A computer malware that encrypts the storage media and files on electronic devices like mobile phones, laptops, desktops, etc., by taking control over the data/ information as a hostage. • The aggrieved are demanded ransom to get his information/ data decrypted or else they are threatened to even sell the data/ information on the dark web. |
|
WORMS, VIRUS & TROJANS
|
• Virus is a program to enter one’s computer and damage and/or alter the files and/or data and replicate it. • Worms are malevolent programs that make multiple copies of themselves on the local drive and network shares, etc. • Trojan is a dangerous program. Unlike viruses, trojan horses do not replicate, but are destructive. Trojan opens a backdoor entry to one’s computer which allows malevolent users to access the system, allowing confidential and personal sensitive information to be stolen. |
|
CYBER-SQUATTING |
It is an act of trafficking in, registering, or using a domain name to make undue profit from the reputation of a trademark which belongs to somebody else. |
|
CRYTO-JACKING |
An unauthorized way to mint cryptocurrencies through the use of computer resources. |
|
ESPIONAGE |
An act where the information & data is collected from the user without his/her knowledge & permission. |
Investigation of cyber-crimes
For conducting cyber-crime investigation, certain special skills and scientific tools are required without which the investigation is not possible. Due to the Information Technology Act, 2000 (“IT Act”), certain provisions of Criminal Procedure Code and the Evidence Act, have been amended. Along with this, certain new regulations had been enforced by the Indian legal system to meet with the need of cyber-crime investigation.
-
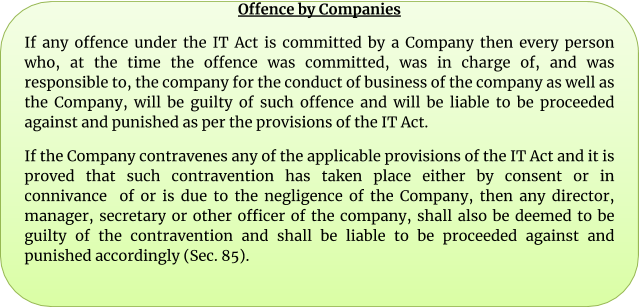
Who can investigate?
The power to investigate the accused in regard to the cyber offences, has been entailed in Section 78 of the IT Act, which says that “notwithstanding anything contained in the Code of Criminal Procedure, 1973, a police officer not below the rank of Inspector shall investigate any offence under this Act”. Nevertheless, the IT Act is not sufficient to meet the necessity, therefore the Criminal Procedure Code, 1978 and the Indian Penal Code, 1860, were also amended accordingly to introduce cyber-crime under their ambit. This gives power to the Inspector to register and investigate the cyber-crime as like another crime.
-
Process of search & arrest
The power of the police office and other officers to enter, search etc. is entailed in Section 80 (1) of the IT Act, which says that, notwithstanding anything contained in the Code of Criminal Procedure, 1973, any police officer, not below the rank of the Inspector or any other officer of the Central Government or State Government authorized by the Central Government in this regard, may enter any public place, search and arrest without warrant any person, who is reasonably suspected of having committed or of committing or about to commit an offence under the IT Act.
Pursuant to Section 80 (2) of the IT Act, any person who is arrested under sub-section (1) by an officer other than a police officer then such officer shall, without any unreasonable delay, take or send the person arrested before a magistrate having jurisdiction in the case or before the officer-in-charge of a police station.
The Government of India had launched the online cyber-crime reporting portal, www.cybercrime.gov.in, which is a citizen-centric initiative, to allow the complainants to lodge complaints relating to child pornography/child sexual abuse material or any content which is sexual in nature. The Central Government has launched a scheme for formulating of Indian Cyber Crime Coordination Centre (I4C)[3] to handle the cybercrime incidents in India, in an inclusive & coordinated manner.
The said scheme has following seven components:
- National Cybercrime Threat Analytics Unit (TAU)
- National Cybercrime Forensic Laboratory (NCFL)
- National Cybercrime Training Centre (NCTC)
- Cybercrime Ecosystem Management
- Platform for Joint Cybercrime Investigation Team
- National Cybercrime Reporting Portal
- National Cyber Research and Innovation Centre (NCR&IC)
The government is also planning to set up Regional Cyber Crime Coordination Centres at respective States/UTs.
By following below-mentioned steps, one can report a cyber-crime online:
Step 1: Go to https://www.cybercrime.gov.in/Accept.aspx.
Step 2: Click on ‘Report Other Cyber Crimes’ on the menu.
Step 3: Create ‘Citizen login’.
Step 4: Click on ‘File a Complaint’.
Step 4: Read the conditions and accept them.
Step 5: Register your mobile number and fill in your name and State.
Step 6: Fill in the relevant details about the offence.
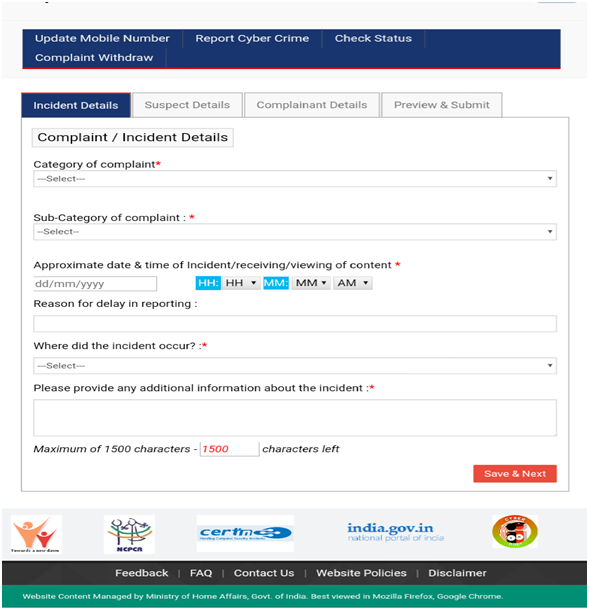
Note: One can also report anonymously.
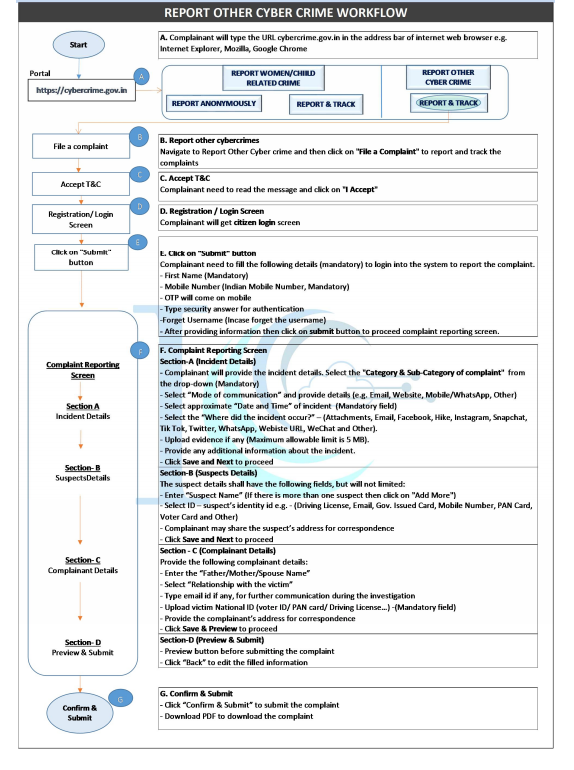
Source: https://www.cybercrime.gov.in/UploadMedia/MHA-CitizenManualReportOtherCyberCrime-v10.pdf
One can report a cyber-crime by:
- Filing a written complaint in nearest, any Cyber Cell
- Lodging an F.I.R (First Information Report)
- Filing a complaint at https://www.cybercrime.gov.in/Accept.aspx
After filing of a complaint / F.I.R., the process of investigation, is hereby diagrammatically presented below:
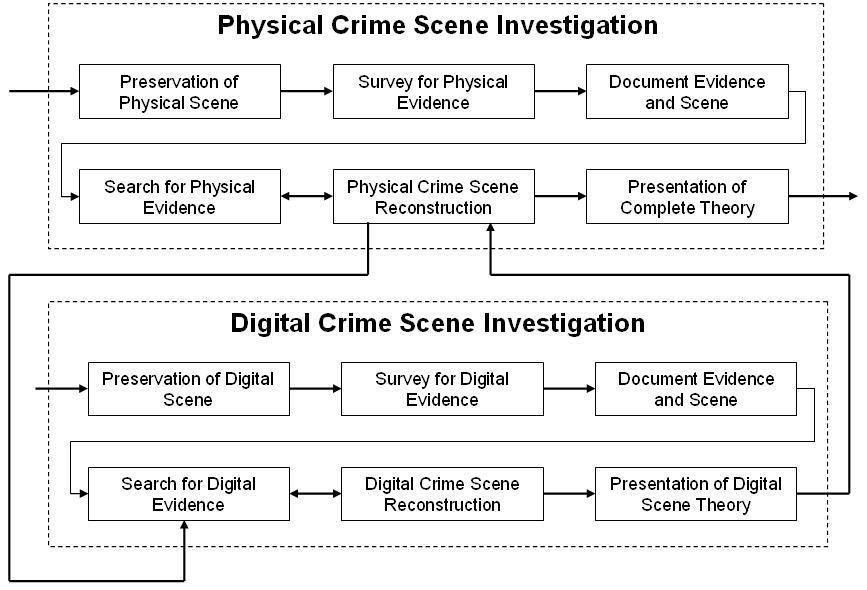
Source: http://www.dynotech.com/articles/images/crimescene.jpg
In case the response has not been appropriate then the complainant can write to State / UT Nodal Officer and Grievance Officer, the details of which can be accessed here: https://www.cybercrime.gov.in/Webform/Crime_NodalGrivanceList.aspx.
Recently, for Delhi only, a new feature “Citizen Financial Cyber Fraud Reporting and Management System” has been activated for prevention of money loss in case of Cyber Financial Fraud; for immediate reporting the complainant can Call 155260 (9 AM – 6 PM only) and further details can be accessed from ‘Citizen Manual’ under “Resources Section” at www.cybercrime.gov.in.
Prosecution for cyber-crimes
Some common cyber-crimes incidents which attracts prosecution as per the applicable provisions of the IT Act, are provided herein below:
|
Online hate community
|
It is created for provoking a religious group to act or pass obnoxious/ objectionable remarks against a public figure or the country etc. Applicable provisions: Section 66A of IT Act + 153A & 153B of the Indian Penal Code (IPC) |
|
Email account hacking |
If a person’s email account is hacked and offensive / indecent emails are sent to people who are in person’s address book. Applicable provisions: Sections 43, 66, 66A, 66C, 67, 67A and 67B of IT Act. |
|
Web defacement
|
The Website’s homepage is swapped with a defamatory or pornographic content/ page. Applicable provisions: Sections 43 and 66 of IT Act and Sections 66F, 67 and 70 of IT Act also apply in some cases. |
|
Cyber terrorism
|
The terrorists are using virtual & physical storage for hiding data & records of their illegal business. Applicable provisions: terrorism laws apply + Section 66F & 69 of IT Act. |
|
Phishing and email scams
|
It involves acquiring sensitive information fraudulently by masquerading as a reliable & legitimate entity. Applicable provisions: Section 66, 66A and 66D of IT Act + Section 420 of IPC |
Conclusion
The Indian Computer Emergency Response Team (CERT-In) is the national nodal agency established by the Ministry of Electronics & Information Technology (MeitY), Government of India, for responding to computer security incidents & securing the Indian cyber space. In the year 2019, CERT-In handled 3,94,499 incidents. The incidents handled were:
- Website Intrusion & Malware Propagation
- Malicious Code
- Phishing
- Distributed Denial of Service attacks
- Website Defacements
- Unauthorized Scanning activities and vulnerable service.
The CERT-In has executed a Memorandum of Understanding on cyber security co-operation with Finland, Estonia & South Korea, to strengthen & enable information sharing & collaboration for incidents resolution.[4]
The MeitY has also launched “Cyber Swachhta Kendra”[5] (Botnet Cleaning and Malware Analysis Centre), to detect the botnet infections and create a secure cyberspace in India. This centre is being operated by the CERT-In as per the provisions of Section 70B of the IT Act.
Disclaimer: The data & content of this article is purely for informational purpose on the subject matter. An expert advice should be sought for any specific incident/circumstances.
References
[1] https://www.statista.com/statistics/309435/india-cyber-crime-it-act/
[2] https://economictimes.indiatimes.com/wealth/personal-finance-news/cyber-criminals-stole-rs-1-2-trillion-from-indians-in-2019 survey/articleshow/75093578.cms#:~:text=Rs%20131.2%20million%20is%20the,the%20global%20average%20being%2067%25
[3] https://www.pib.gov.in/PressReleasePage.aspx?PRID=1599067
[4] https://www.cert-in.org.in/
[5] https://www.cyberswachhtakendra.gov.in/
Students of Lawsikho courses regularly produce writing assignments and work on practical exercises as a part of their coursework and develop themselves in real-life practical skill.
LawSikho has created a telegram group for exchanging legal knowledge, referrals and various opportunities. You can click on this link and join:
 Serato DJ Crack 2025Serato DJ PRO Crack
Serato DJ Crack 2025Serato DJ PRO Crack











 Allow notifications
Allow notifications


