This article is written by Mugeera Patel who is pursuing a Diploma in Business Laws For In-House Counsels from LawSikho.
Digital technologies have become the cornerstone of our day to day lives. We exist in an era where there are new applications popping up every month across our screens with the taglines like – “free trial for a game”, “let’s get you an e-book to help you with boredom“ , “Answer a few questions to get your personalized study plan” or “designed exclusively for your needs”.
We as consumers, often tend to give in to such pop ups and download the application or get on the website and agree to all permissions. However, we rarely take a glance at these permissions or user licenses for products before agreeing to it and that is where complications crop up. This is because of the fact that these permissions and user contracts/licenses explicitly state terms of use of the said product.
An example of this can be seen in your universities online library. You will find statements like:
This validation allows HIJ (University name) Libraries registered members to access HIJ Libraries’ E-Resources remotely or something like non-members are prohibited to any types of remote access.
What happens if you share your account out of good-faith to someone in need without reading these terms? You are likely to get in trouble; because of the DRM policies your university might have.
Table of Contents
What is DRM?
Digital Rights Management (DRM) are a set of tools that enable developers of technologies and software interfaces to create digital restriction mechanisms with the help of copyright protection to overcome acts that could harm the value of a product in the market e.g. piracy, unauthorized usage and modification to the product.
How does DRM work?
DRM acts as a supplementary safety device for copyright holders by allowing them to retain control over their assets through various technologies. It acts as an extra layer of authorization and validation working to strengthen the valuation of copyrighted materials in the market.
What are different types of DRM technologies and methods and their usage?
1.) Permissive/Restrictive Licensing agreements
Licenses give users a right to do or refrain from doing certain activities when it comes to the usage of products. By means of copyright protections; a permissive license is the one that allows slight modification in the manner of its usage and also gives rights with regards to what can be done to what extent. It usually gives information as to whether the original code of the product can be modified or redistributed with changes.
Restrictive licenses are those which prohibit any changes to the product and its source code and is one of the most common types of DRM method used by the majority of the companies. This is done to ensure that the product they are selling is used for the purpose it is intended. This purpose will be clearly specified in the terms of use. E.g. When you buy an educational course online there is a disclaimer accompanied with it which says that usage of the material for any viable commercial purpose is strictly prohibited. If a person tries to use it for any unauthorized means companies can track the person through their sources and they will have to pay relevant fines and damages.
Recently, a leading service provider that trains foreign lawyers for qualifying into the UK as lawyers deployed officers to track any such breaches and unauthorized usage of study materials. This is because these materials are copyrighted under relevant laws and any usage that is unauthorized, harms the money- making capacity and goodwill of the business and puts its brand name in a serious risk.
Let’s take a look at what a licensed restrictive usage clause in terms of usage of a product can look like
Use of a method of DRM Use of tools of DRM
↓ ↓
Any circumvention of technological methods or encryptions or digital rights management systems to access, print or download content are going to be susceptible to be prosecuted under applicable laws.
Clear usage of purpose of license
↓
The content is licensed only to the academic student of the certificate course, sharing of login details with the other person isn’t permitted. Any such attempt will cause immediate disconnection and removal from course notwithstanding anything during this agreement. ↑
Penalty for breach of license
**- Sample clause based of LawSikho’s Terms of Use on the website
The most important elements to understand and specify in this types of clauses are
a.) The kind of method used : As seen in the above example the first part specifies the method and tools used; this knowledge will shift the onus from the company to the user as the company has fulfilled their intent and obligation by making the customer aware of the purpose of usage of the product. A key term here is ‘circumvention’ this is because breach of this copyrighted material can happen in various forms and is not restricted to one. Stating circumvention in this type of clause helps company gain a foothold over any and all forms of prohibited usages by the customers
b.) Who is the product licensed to : Specification of this will help clear documentation in case any dispute arises as to who was using the material. If this is not specified the user can contend that they obtained the product for sharing among themselves and the company will have no contention to withhold on their behalf
c.) Penalty for breach of the license : This enables the users to be aware of the risk entailed with unauthorized usage of the product
2.) Use of Encryption and decryption keys
Encryption and decryption work like letters written with invisible inks that can only be accessed on usage of a particular chemical, lights or glasses. E.g. If you were to buy Taylor Swift’s new merchandise CD which was in collaboration with Sony or any other CD- player brand and it used the process of encryption and decryption; then you would only be able to use it on a particular CD player and not on the CD-ROM of your computer. How this works is the CD would contain secret messages in form of codes that would only be accessed through the music player of the particular brand which would contain links that make complete sense of the code and would act as the right chemical for music.
Companies use this tool of DRM to restrict access and limit the usage of the customers to one.
3.) Verifications according to technologies:
a.) Limited install activations
This type of DRM technology limits the number of installations with regards to a product. This technology tries to prevent replication by requiring verification each time it is installed or used on a device.
An example of this is the OTT platforms and their pricing plans. Netflix has various plans that clearly mention the number of devices allowed which range from one and go-up to four. These platforms also have certain restrictions as to who can download and save offline. If the platform detects any unauthorized usage it generates disclaimer of too many people using it. This helps them retain control and track usage
b.) Persistent online authentication
This type of authentication requires users to enter their details every time they log-out of a device. A very common example of this is seen on websites that requires users to create an account for accessing the website. While signing in; users mostly have the option of the checkbox that displays remember me. If users choose this option their details are stored with the help of a cookie and the next time they visit a website they are automatically signed in.
Examples of this type of authentication are seen of Facebook, Gmail and Amazon along with many other websites. This type of authentication helps companies create a form of digital identity for users which helps them monitor the usage of the accounts for any illicit activities. On social media this also helps in flagging for content that is spam by reporting the account.
4.) Copy restrictions
We often come across documents and research papers on the internet that do not allow us to copy- paste the content or rather make it extremely hard to do so this is to create copy restrictions. This type of DRM method is also used in the case of books. Publishers of books implement this tool to ensure that there are no illegal copies being sold and reproduced or to ensure that there is no circumvention in the usage of products that are protected by relevant copyright laws.
An interesting case study arose under this when a foreign student in the USA, brought cheaper but permitted copies of textbooks in his resident home country. He then brought it to the US and sold it to his fellow classmates making a huge profit. The price difference between the U.S. and the student’s country was so vast that it led to him making a lot of money. However, the company soon caught a whiff of this and sued him in the US Court of Appeals and were awarded damages of a whopping $600,000. *(1)
5.) Anti tampering
Anti-tampering method disclaimer or software is a tool of DRM that creates additional layers of authorization and makes it difficult to modify the code. This type of tool is used in applications, financial website interfaces, websites, and games in the form of codes. This method is used to restrict actions like subverting of validation for a software and putting in code for data theft.
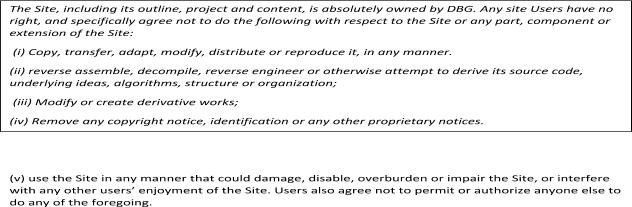
This type of method is also used on various websites and is clearly mentioned in its terms of use as follows:
6.) Regional Lockouts
Regional Lockouts are when certain areas or sections of the world are deprived of a particular product. E.g. There have been numerous times when various websites pop apologetic disclaimers like “this cinematic production can’t be viewed in your region” or the access to this video library can be done only in the U.K”. This is mainly done because licenses pertaining to the particular film or song may be obtained for one region only and are deemed invalid in another region, for it to be displayed in another area than where it was licensed an entirely new deal has to be chalked up with the executives of specific region. E.g. When Spotify was to launch in India any licenses or term of usage made specifically for Europe would have to be re-negotiated as per licensing requirements in India
This type of tool allows the company to control the availability, timeline, distribution and also limit piracy. In terms of business strategy it also creates a buzz around the product
DRM and its existence across copyright Laws in various countries
India: The existence of measures against circumventions is found in Indian Copyright Act, in its amendment of 2012. Currently section 65- A of the Act provides for a punishment of two years of imprisonment and a penalty where liable to any person who tries to circumvent any rights convened under the Copyright Act to any person with the intention of infringement. The act further goes on to list the exceptions in 65-B as follows
a.) Consenting to all that is not explicitly prohibited by the act. However this exception is quite ambiguous when taking into consideration a group of people trying to find loopholes and using it.
b.) For the purposes of conducting investigation as prescribed by the law
c.) Security testing or computer system or network testing; which is done mainly in all business and their I.T. departments and I.t sector companies
d.) Cases where there is a need to circumvent technologies to establish user identification or surveillance of users
e.) For the purpose of national security
In 2016, there was a case in High Court of Delhi between Tata Sky and YouTube, where Tata Sky approached the court because YouTube had a video uploaded on its problem showing how to circumvent Tata sky’s technology titled ‘Hack Tata Sky exclusive’ showing how to hack the set top box and watch HD channels for free, Tata sky also contested that there was trademark infringement by displaying the video inclusive of Tata’ sky’s trademark. The court held that the video should be removed, however a clear distinction was not made as to whether this case was on infringement or circumvention of technologies. (2)
U.S.A: DRM has a very strong foothold in the business ecosystem as well as protection wise in the US Copyright regime. Its first appearance in the legislation dates back to 1998. Where an amendment was passed to the Digital Millennium Copyright Act.
The DMCA currently lays down provisions that focus on prohibiting circumventing, restricting and forbidding unauthorized access and usage of copyrighted works under the Act. There is a clear cut distinction as the access control and the user control.
It goes a step further to restrict the manufacturing of any part that may assist and aid in the ability of any form of circumvention. It further lays down the clear and concise definition of what it means to circumvent as a technological measure and goes on to provide exemptions for nonprofits, libraries or educational purposes, encryption and security testing among a few others like fair use and doctrine of first sale. Further the copyright regime of US also has the option of take down notice under the DMCA which Section 512 (c) to restrain any financial gains of advertisers or companies with the content of copyright holders.
The legislators and activists however believe that this list of exceptions is constrained and has been hugely controversial due to its restrictive nature. Whether a particular aspect is circumvention of technologies is to be decided on a case to case basis.
One of the biggest controversies associated with it happened soon after the act came into existence.
In 2001, A Russian National Dmitry Sklyarov, who was a programmer, built a software program back in Russia which allowed to convert adobe ebooks to normal pdf e-books and enable users to read without paying. This was deemed to be legal in Russia and created before he signed an employment contract with adobe. Adobe took cognizance of this after he spoke at a security conference and claimed under the DMCA that this program would circumvent Adobe’s technologies and DRM code imbibed in the books. Under this law Sklyarov could have faced 5 years of imprisonment and close to 1.2 billion in fines. However later the case was said to be dropped citing that this was a short-sighted strategy for applicability of DMCA, but he had to forfeit his passport. This created a havoc in the research community and there were protests on the streets. From then on until today the Provisions of DMCA and DRM are feared of and are said to be bad for the industry. As seen above it’s a part which is allowed the exception however the extent of it is not duly defined (3)
European Union: The EU legislation seeks to create a balance between policymaking and the rights of copyright holders.
Existence of protection of DRM finds its way in the EU through the Information society directive. This directs the EU member states to apply the provisions of WIPO treaties to their legislative regimes.
Further this type of provision is also found in the copyright directive which states that circumvention of DRM and operating of devices with such type of circumvention is prohibited. An e.g. root (jailbreak devices) we use.
The EU defines DRM as an effective technological measure in its Copyright Directive under articles 6 and 7. The EU does not have a distinction of access control and user control options and instead of deciding case to case decides on a three step test. Further the exceptions with regard to private copying is one of the stark different features of DRM in the EU.
The three step test finds its origin in the Berne convention of 1967 and this three step test is seen in many multilateral trade agreements between countries. This test seeks to apply uniformity to applications and situations when deciding what could be used as fair use. The three step test provides as follows:-
It is a matter of the legislation in countries of the EU to allow reproduction of works for certain special cases, provided that such re-production does not conflict with the normal exploitation of work and does not prejudice the interest of the author.
This test only finds its applicability and sheds light to the rights of reproductions and does not give information about any other exclusive rights associated with the copyrights.
This test too, has been deemed restrictive and has been interpreted by the World Trade Organization, which one suggested close to 2000 exceptions but these exceptions never find ways to multilateral agreements (4)
The Many facets of Arguments for DRM
The Good
- Concentrates market power in the Hand of the producer/ Author
Digital rights enable the author to ensure the ability to distribute their work is with in accordance with their own terms. It helps the author to do so by embedding technologies within the product and limiting the access to paid copies only. This is of great use when an independent artist or author takes the decision to self-publish a book or produce music for a particular region. It helps the author create various payment models for the product without interference of management and executives. It also helps retain the moral rights of the author to the fullest extent possible. Moral rights provide a balance between the conflict of best price for consumers and economic interest of the Author
The Bad
- The Lack of Interoperability
Interoperability refers to accessing a technology or product across various means. This provides consumers value for their money and enables them to use it as and how they want. However if a device has an element of DRM this type of free usage will become impossible. This limits the private enjoyment rights of the buyer. This factor is clearly mentioned in the terms of use and rests the onus on consumers when buying products.
Brands are often subjected to heat due to this inoperability. An example of this is the Norway Ombudsman ruling in 2009 where the Consumer Ombudsman criticized the policy of Apple for only allowing reproduction of music only on iphones. However Apple did not budge at the time to give into the criticism. (5)
- The ambiguity of contracts and DRM penalize the common man to a great extent
Existence of DRM in a product or services changes the scope of the contract between private parties to that of a more commercial transaction which binds the consumers and provides sanctions on usage other than the intended purpose. Further if protected by DRM simple actions like downloading for private use can turn into mistakes too if accounted for in the USER contract.
- A seeming conflict between fair use and DRM technologies exists because of the hazard it causes for doctrine of fair use and the invalidation of the defense of first sale. (6)
The Ugly
DRM provides an opportunity of mass surveillance of user data which by its very existence is against the privacy right of individuals. Since data draws comparisons to human rights today, in recent times any potential of a breach is to be averted. However DRM increases the chances of breach and surveillance by providing copyrighted users identity of users of their products this helps unauthorized usage and circumvention but it also puts consumers at risk.
Examples of this is the Vodafone Greek wiretapping case which lead to tapping of phones of close to 100 Greek officials by using a rootkit phone, Vodafone was fined about 75 million for the breach. (7)
Another similar suit was followed in Zambia Africa where two journalists filed a suit against Airtel for phone tapping in 2015 which is currently on-going. (8)
Conclusion
There is a need of balance between the interests of all stakeholders i.e. Companies with DRM technologies, copyright holders and the consumers. Currently the market hails that there is nothing positive about the DRM situation, however there are very few DRM free options available to the consumers. New methods should be experimented with in the rights management system by research in usage of smart contracts, block chain for managing rights and licensing (E.g. Sony in 2018 announced a right management system built using the block chain) (9) and lastly user awareness. An all-encompassing solution would be standardization of DRM processes which clearly defines the mechanisms of applications, goals, and security and contract requirements stated in the user contract itself. This will give rise to accountability for the current problems.
References
- https://www.supremecourt.gov/opinions/12pdf/11-697_4g15.pdf
- https://indiankanoon.org/doc/166344020/
- https://en.wikipedia.org/wiki/United_States_v._Elcom_Ltd.
- https://www.wto.org/english/tratop_e/dispu_e/1234da.pdf
- https://casetext.com/case/apple-ipod-itunes-antitrust-litigation
- ** Picot Arnold, Marina Fiedler, and Impacts of DRM on internet Based Innovation, in E. Becker et al. (Eds.): Digital Rights Management, LNCS 2770, pp. 288-300, 2003, and Springer-V
- https://www.spinellis.gr/pubs/jrnl/2007-Spectrum-AA/html/PS07.pdf
- https://www.zambiawatchdog.com/zicta-probles-airtel-over-phone-tapping/
- https://www.sony.net/SonyInfo/News/Press/201810/18-1015E/
Other reading materials
- http://jiplp.blogspot.com/2012/12/indias-new-copyright-law-good-bad-and.html
- https://www.ftc.gov/sites/default/files/documents/public_statements/different-perspective-drm/rosch-berkeley-drm20speech-mar9-2007.pdf
- https://copyright.gov.in/Copyright_Act_1957/chapter_xiii.html
- https://en.wikipedia.org/wiki/Digital_rights_management
Students of Lawsikho courses regularly produce writing assignments and work on practical exercises as a part of their coursework and develop themselves in real-life practical skill.
https://t.me/joinchat/J_0YrBa4IBSHdpuTfQO_sA
Follow us on Instagram and subscribe to our YouTube channel for more amazing legal content.
 Serato DJ Crack 2025Serato DJ PRO Crack
Serato DJ Crack 2025Serato DJ PRO Crack











 Allow notifications
Allow notifications


