In this blog post, Yamini Sharma, a student pursuing a Diploma in Entrepreneurship Administration and Business Laws by NUJS, critically analyses the various benefits specified for MSMEs under the Micro, Small and Medium Enterprises Development Act, 2006.
Introduction
The Micro, Small and Medium Enterprises Development Act, 2006 (“MSMED Act”), was enacted by the Government of India on June 16, 2006, primarily for the promotion, development, and enhancement of the competitiveness of Micro, Small, and Medium Enterprises (“MSME”). In the recent years, MSME has emerged as a dynamic sector of the Indian economy. The MSMED Act provides a legal framework to the concept of Enterprise, which includes manufacturing as well as service sectors. The MSMED Act also provides for the establishment of a National Board for Micro, Small, and Medium Enterprises, measures for promotion, development and enhancement of competitiveness of micro, small and medium enterprises, procedure for filing of memoranda, credit facilities, procurement preference and provisions related to delayed payments to micro and small enterprises, preference in Government procurements to products and services of the micro and small enterprises.
Definition of Micro, Small and Medium Enterprises
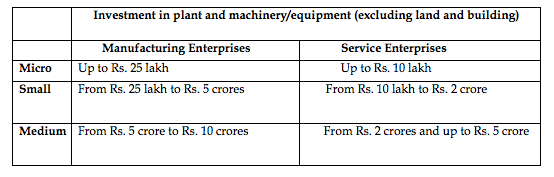
Under the MSMED Act, Enterprises have been classified broadly into two categories, namely enterprises engaged in the manufacture/production of goods about any industry; and enterprises involved in providing/rendering of services. Enterprises have been defined regarding investment in plant and machinery/equipment (excluding land & building), as per the below table:
Furthermore, in calculating the investment in plant and machinery, the cost of pollution control, research and development, industrial safety devices and such other items as specified by notification shall be excluded.
Benefits to the MSME’s
The Government of India through its various subsidies, schemes, and incentives promote MSMEs through the MSMED Act. To avail these benefits, Registration under the MSMED Act is required. The act provides the following benefits/incentives to the MSME’s:
- Preference in procuring Government tenders: The Government of India, through its Public Procurement Policy for Micro and Small Enterprises Order, 2012 (“Public Procurement Policy”) provides that all Central Government Ministries, Departments, and Public Sector Undertakings shall procure minimum of 20 percent of their total annual value of goods or services from Micro and Small Enterprises, which has become mandatory from April 1, 2015. As per the Public Procurement Policy, Micro and Small Enterprises having registration with District Industries Centre or Khadi and Village
 Industries Commission or Khadi Village and Industries Board or Coir Board or National Small Industries Commission or Directorate of Handicrafts and Handlooms or any other body specified by Ministry of MSME (“Ministry”) are provided certain benefits under the Public Procurement Policy. However, vide Press Release dated 18th February 2016, for ease of registration of MSMEs, the Ministry has started Udyog Aadhar Memorandum which is an online registration system and all Micro and Small Enterprises having Udyog Aadhaar Memorandum shall be provided all the benefits available for Micro and Small Enterprises under the Public Procurement Policy.
Industries Commission or Khadi Village and Industries Board or Coir Board or National Small Industries Commission or Directorate of Handicrafts and Handlooms or any other body specified by Ministry of MSME (“Ministry”) are provided certain benefits under the Public Procurement Policy. However, vide Press Release dated 18th February 2016, for ease of registration of MSMEs, the Ministry has started Udyog Aadhar Memorandum which is an online registration system and all Micro and Small Enterprises having Udyog Aadhaar Memorandum shall be provided all the benefits available for Micro and Small Enterprises under the Public Procurement Policy.
- Protection against the delay in payment from Buyers: The MSMED Act provides protection to Micro and Small Enterprises from delayed payments. It specifically provides that where a Micro and Small Enterprise supplies any goods or renders any services to a buyer, the buyer is required to make the payment on or before the date agreed upon by them and in no case, the period can exceed 45 days from the date of acceptance.
- Right of interest on delayed payment: In the case where the buyer fails to make the payments, he shall be liable to pay compound interest with monthly rests to the supplier on that amount from the date falling after the due date, at three times of the bank rate notified by the Reserve Bank of India.

- Time-bound resolution of disputes with Buyers through conciliation & arbitration: MSMED Act provides that in case of any dispute arising out of non-payment of dues, Micro and Small Enterprises may refer the dispute to the Micro and Small Enterprises Facilitation Council, which shall conduct conciliation in the matter and where such conciliation does not give fruitful results and is terminated without any settlement thereof, the Council may itself take up the dispute for arbitration or refer it to any institution or centre providing alternate dispute resolution services.
Further, the MSMED Act also provides for the constitution of National Board for Micro, Small, and Medium Enterprises, which is an apex advisory body constituted to render advice to the Government on all issues about the MSME sector. The Minister of MSME is the Chairman, and the Board comprises among others, State Industry Ministers, some Members of Parliament, Secretaries of various Departments of Government of India, financial institutions, public sector undertakings, industry associations and eminent experts in the field. The board meets periodically to take stock of the issues about policy matters.
Registration
The Registration process of an MSME requires the filing of an Entrepreneurs Memorandum (“EM”) with the District Industries Centre (“DIC“) of the concerned area, after which, DIC shall issue an acknowledgment along with an EM number.
As a part of its recent initiatives, for the ease of registration of MSMEs, the Ministry vide Press Release dated 18th February 2016, has started Udyog Aadhar Memorandum which is an online registration system.
References:
- http://msme.gov.in/
- http://dcmsme.gov.in/notification.pdf
- Office memorandum, Ministry of Micro, Small & Medium Enterprises, Press Release dated 18th February 2016.
- The Micro, Small and Medium Enterprises Development Act, 2006









































 Allow notifications
Allow notifications


